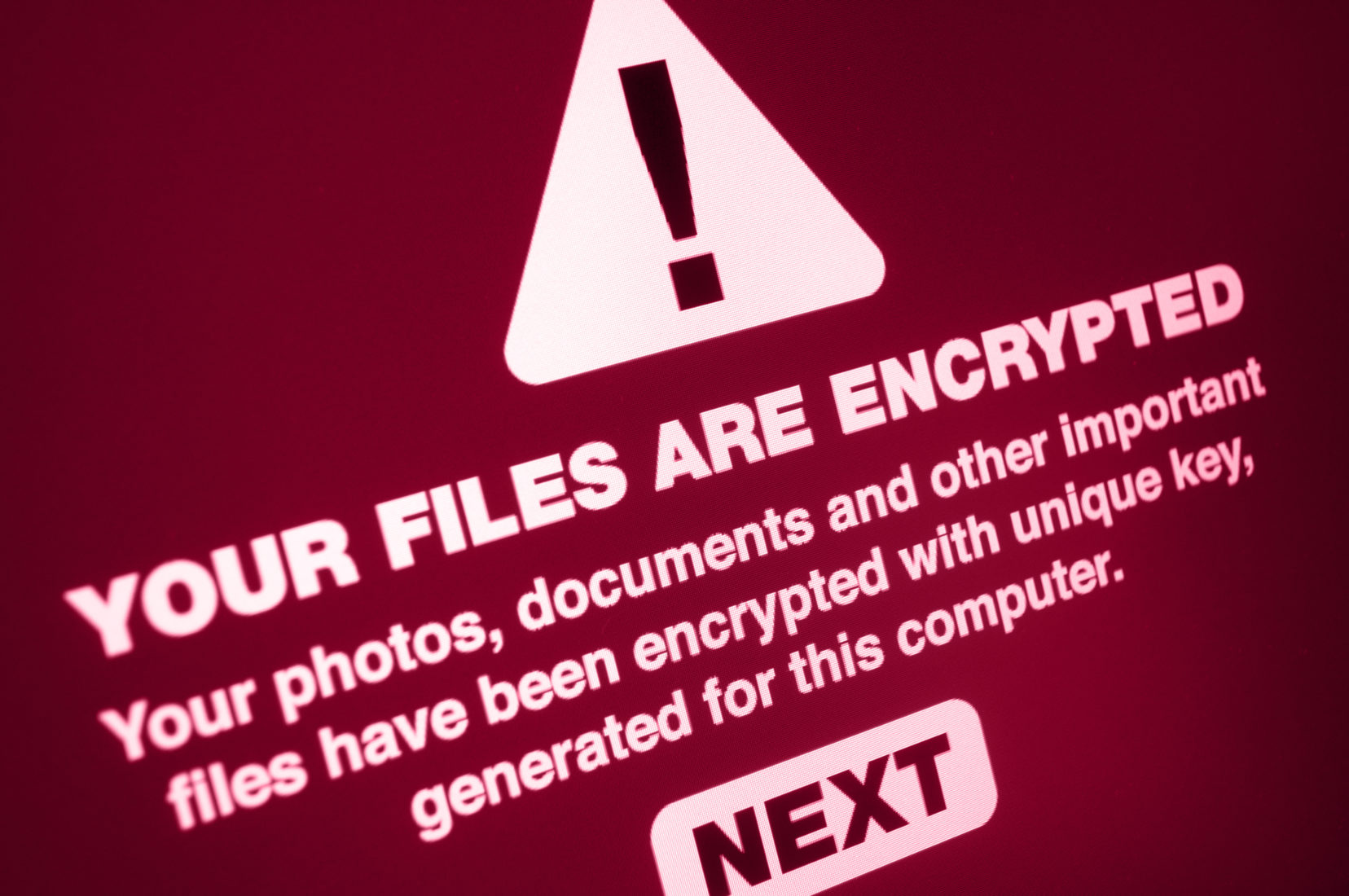
In May 2017, the UK and the rest of the world witnessed arguably one of the most devastating cyber-attacks ever known to have taken place.
WannaCry was estimated to have affected more than 200,000 computers in over 150 countries; the aftermath of the ransomware cryptoworm lasted for days and even weeks, and most famously brought over a third of UK’s NHS Trusts to a standstill.
After every cyber-attack there’s usually a lesson to be learned so that it can be prevented from happening again. Historically, the NHS was never viewed as a prime target for cyber-hackers. It’s commonly accepted that large businesses or banks would be more lucrative and appealing prospects.
But threat actors have other targets in mind now.
With data quickly becoming a new currency and organisations dependent on being able to not only provide, but access, digital services too, every organisation or industry body now has a target on their backs.
The slightest hiccup in the delivery and access to services, or whisper of a data leak, can not only leave an organisation unable to perform its duties, but can also leave them financially and reputationally damaged.
If hackers get hold patients’ data, they could hold a hospital to ransom or resort to ‘social engineering’ techniques
The services the NHS provides are critical. It can ill afford any ‘blackouts’ not just because of the risk it poses to patients, but also the monetary implications for the NHS too. Secondly, patient data is very valuable.
If hackers can get hold patients’ data, they could hold a hospital to ransom or resort to ‘social engineering’ techniques (the gathering of information like an email address or phone number to procure even more access to important accounts).
After WannaCry, the NHS (or any public service organisation for that matter) would ever be under the falsehood that cyber-hackers would not be interested in disrupting them. What WannaCry unearthed was how much disruption to its digital services could have on the day-to-day operations of its Trusts.
One year on, what have we learned?
The need for tighter rules with employees
The majority of online threats are web- and email-based and occur due to people not understanding the security implications of their actions. There are huge risks involved when employees take their corporate hardware home; WiFi at home is nowhere near as secure compared to a healthcare establishment (in most cases) and good security practice is often an afterthought (if at all) for many citizens.
Employees are now risking so much more with advanced viruses and trojan horses abound. New ransomware can detect where that computer is on that network, and sit there waiting ready to strike.
When the computer is plugged back in the ‘corporate network’ at work, it can spread across the entire system before activating, causing havoc for thousands of users.
Even new software is vulnerable. The new NHS Mail 2 system was designed to be accessible outside of the hospital.
The risks with this system, however, are that emails that can be accessed from outside the organisation can be susceptible to phishing campaigns, due to a lack of security control. If an employee were to click on a phishing link, hackers could access details, personal information and passwords.
The importance of user education
Everyone knows (or should know) nowadays not to share their bank cards details or passwords. However, not everyone seems to adhere to this in the workplace.
Organisations – including the NHS – need to remember that not everyone is an IT expert. User education is the hardest thing to do, particularly involving the training of large numbers of people.
Organisations therefore need to provide their employees with the level of understanding needed, to ensure that everyone knows how to work safely and securely and won’t be susceptible to prying threat actors.
How to shore up security in healthcare establishments
With the NHS and its Trusts in a constant battle over budgets, it has limited funds to spend on its security, but it is an investment that needs to be made. They need to do so intelligently, and not just throw money at the problem.
Each Trust needs to review its internal security systems to ensure they have a layered security defence spanning encryption, firewalls, web filtering and ongoing threat monitoring as well as a proactive stance against threat actors.
WannaCry shocked the world and left many in fear about what a cyber-attack could do to people’s day-to-day lives. The ramifications of the event could have been far worse.
Where a cyber-attack could cost as much or more than a natural disaster to fix, protecting the country’s basic infrastructure in the face of cyber criminals needs to be a priority.
What the NHS could learn from 2017’s WannaCry attack
David Navin, head of healthcare and enterprise at Smoothwall, reflects on the lessons of the ransomware attack that affected more than 200,000 computers in over 150 countries and brought more than a third of NHS Trusts to a standstill.
David Navin
IFSEC Insider | Security and Fire News and Resources
Related Topics
New app launched to enhance mandatory fire safety training in the NHS
Protecting health workers is a complex challenge, but emerging strategies show promise
Six companies charged with fire safety offences for blaze which destroyed Cheshire retirement village